More than an access point
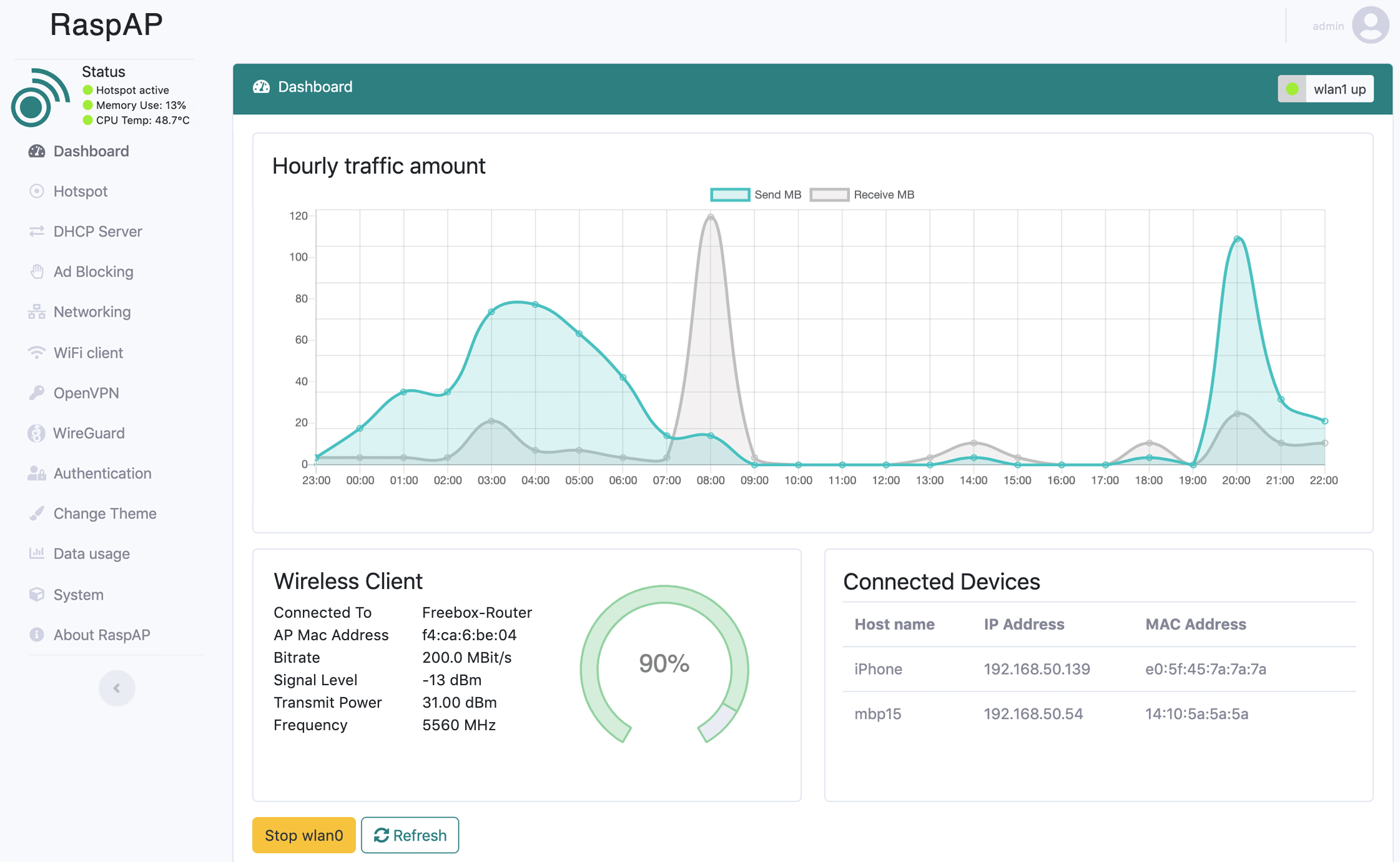
RaspAP is feature-rich wireless router software that just works on many popular Debian-based devices, including the Raspberry Pi.
Customizable, mobile-friendly interface in 20+ languages. Sets up in minutes.
Multiple VPN options
Popular OpenVPN, cutting edge WireGuard and Tailscale encrypted tunnels may be configured to securely connect your client devices.
Ad block integration
Streamline AP throughput for your clients by sending requests for ads, trackers and other undesirable hosts to DNS blacklist oblivion.
Bridged mode
Want your upstream router to assign IP addresses? RaspAP lets you change the default routed configuration to an alternate bridged AP mode.
Easy to customize
Modify RaspAP to suit your needs with a completely exposed default configuration, many installation options, themes and more.
Docker ready
Deploy RaspAP quickly in a portable, lightweight and isolated Docker container for all your application needs.
Made for IoT
Small on memory utilization yet big on features, RaspAP is ideal for IoT applications where wireless connectivity and data sharing are a must.
Integrated API
RaspAP includes support for stateless client-server data exchange via a high performance RESTful API based on FastAPI.
Custom user plugins
Want to extend RaspAP's functionality? A plugin manager and sample plugin make it easy for developers to create their own custom plugins.
VPN provider control
Administer several of the most popular VPN providers via their Command Line Interfaces (CLIs) directly in RaspAP's UI.
Additional Features
Data usage graphs for all interfacesSSL certificate support
Captive portal integration
Up-to-date security audits
Advanced DHCP server control
802.11ac 5GHz operation
Dynamic DNS support
Auto-detect external wireless adapters
WPA3-Personal + 802.11w support
Docker support
Fully responsive + mobile-ready
Get Started with RaspAP
Our frequently asked questions (FAQ) are continuously updated and are a great place to start. Need help not covered in the FAQ, have an idea or want to share your project with the RaspAP community? Head over to our GitHub Discussions or join our Discord. For everything else and more detailed information, dive into our official documentation.